
12 Things to Do, See, and Eat While at Rocky Mountain Cyberspace Symposium (RMCS) Feb 2-5
January 26, 2026
How Trellix Mobile Security Enables Compliance with DISA STIG Mandates for Mobile Security with Android 16 and iOS 26
February 12, 2026A 5-Step Guide to Third-Party Risk Management (TPRM) for the U.S. Public Sector and Higher Education
Whether you are a Federal agency, a State or Local department, or a Higher Education institution, your mission depends on external partners. Organizations increasingly rely on these “third parties” to bridge gaps in technical capacity, drive innovation, and scale services with cost-efficiency.
This ecosystem includes every external entity that touches your operations—from the janitorial staff and office supply vendors to critical cloud infrastructure providers like AWS or Azure, and specialized SaaS platforms for case management or finance.
Third-Party Risk Management (TPRM) has evolved from a potentially arduous compliance task into a strategic necessity for mission readiness. At FRC, we understand that managing these risks is not just about security; it is about protecting the public trust. To address these challenges, FRC has strategically partnered with TrustCloud, a leader in AI-native TPRM. Together, we deliver a modern, automated approach to risk that integrates seamlessly into an enterprise-grade Governance, Risk, and Compliance (GRC) platform.
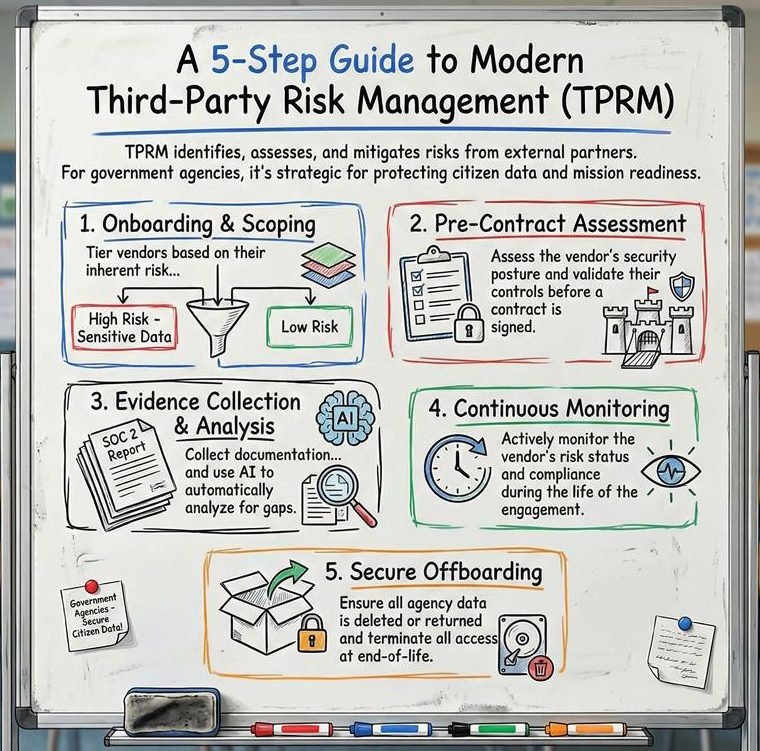


5 Typical Processes in Conducting Third Party Risk Management (TPRM)
Third-Party Risk Management (TPRM) is the process of identifying, assessing, and mitigating the risks presented by an organization’s external partners. TPRM for the public sector is unique due to the high stakes involved—sensitive citizen data, national security interests, and strict regulatory mandates such as NIST SP 800-171 or CMMC. The successful execution of a TPRM program requires a structured lifecycle that integrates procurement, cybersecurity, and mission-owner perspectives. This process begins with the identification of a need and continues through the termination of the vendor relationship.
Step 1: Identification and Inventory Management
An organization cannot manage risk it does not see. The first step in any TPRM program is the development and maintenance of an exhaustive inventory of all third-party relationships. NIST SP 800-161 emphasizes that this inventory should include not just the vendor’s name, but the services provided, the type of data accessed, and the criticality of the vendor to the organization’s mission.
Step 2: Risk Categorization and Impact Analysis
Once a vendor is identified, agencies must categorize the relationship based on the potential impact of a security failure. This involves using FIPS 199 guidelines to assess the potential for harm to the agency’s mission, image, or reputation if the third party’s confidentiality, integrity, or availability is compromised. This phase determines the level of due diligence required; a high-impact vendor will undergo significantly more scrutiny than a low-impact one.
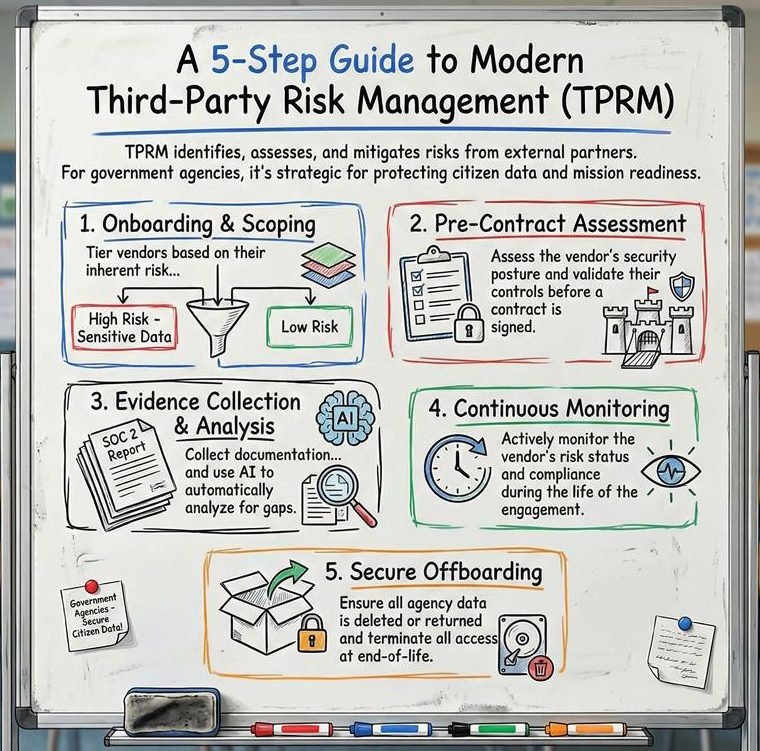
Step 3: Due Diligence and Pre-Contractual Assessment
Before a contract is signed, the agency must perform a thorough assessment of the vendor’s cybersecurity hygiene. This typically involves:
- Questionnaires: Utilizing standardized and customized forms to gauge a vendor’s internal policies and controls.
- Artifact Review: Examining the vendor’s previous audit reports, SOC 2 attestations, or other cybersecurity documentation.
- Security Ratings: Using external, data-driven security rating platforms to quantify the vendor’s real-time security posture and identify indicators of compromise.
Step 4: Contractual Integration and Flow-Down Requirements
The procurement process is the primary mechanism for enforcing security standards. Contracts must explicitly define security requirements, incident notification timelines, and the agency’s right to audit the vendor. A critical component of modern TPRM is the “flow-down” requirement, which mandates that the prime contractor ensures its own subcontractors and sub-suppliers meet the same security standards. This addresses the systemic risk of the Nth-party supply chain.
Step 5: Authorization and Continuous Monitoring
Continuous monitoring is essential to detect changes in the threat landscape or the vendor’s environment. This includes monthly or quarterly reviews of vulnerability reports, tracking the remediation of gaps in the POA&M, and monitoring for new threats using real-time dashboards.
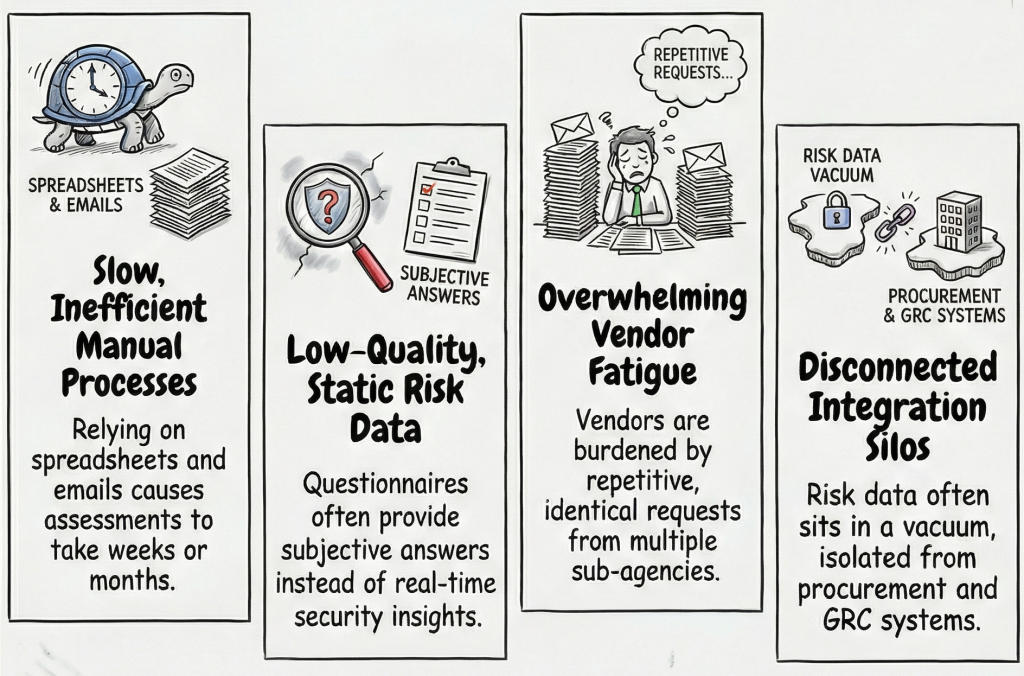
Challenges in Traditional TPRM
Many government agencies and higher education institutions struggle with legacy TPRM methods that are no longer scalable. Common hurdles include:
- Inefficient Manual Processes: Relying on spreadsheets and email leads to long turnaround times—often weeks or months—for a single vendor assessment.
- Low-Quality Risk Data: Static questionnaires often result in incomplete or subjective answers that provide little real-time insight into a vendor’s actual security posture.
- Vendor Fatigue: Vendors are often overwhelmed by repetitive, identical requests from different sub-agencies within the same state or federal department.
- Integration Silos: Risk data often sits in a vacuum, disconnected from procurement systems or the broader Governance, Risk, and Compliance (GRC) landscape.
Why Modern Tools like TrustCloud are Critical for Modern TPRM
In today’s threat landscape, point-in-time assessments are insufficient. Tools like TrustCloud are critical for several reasons:

- Velocity and Scale: By automating workflows, agencies can reduce assessment turnaround times by up to 70%, allowing for faster procurement without sacrificing security.
- Evidence-First Assurance: Modern TPRM moves from “trusting” a questionnaire to “verifying” with data. For example, TrustCloud’s AI can read a 100-page SOC 2 report and instantly flag findings that satisfy specific agency controls.
- “Verify Once, Share Many” Model: TrustCloud supports a unified vendor identity. If one agency assesses a common vendor (like ServiceNow), that assessment can be shared across the entire organization, eliminating redundant work and ensuring consistent security standards.
- Continuous Monitoring: Risks don’t sleep. Modern tools provide immediate alerts if a vendor’s security posture degrades or if a new incident is reported, allowing for proactive mitigation rather than reactive cleanup.
At FRC, we are committed to helping government organizations modernize their risk oversight. By combining our deep public sector expertise with TrustCloud’s AI-driven platform, we empower agencies to build a culture of trust and resilience.
Contact us to learn how we’re helping government agencies and Higher Education institutions. Learn more about TrustCloud’s GRC Platform and How Continuous Monitoring and Validation Actually Work in Governance, Risk, and Compliance (GRC) Tools



