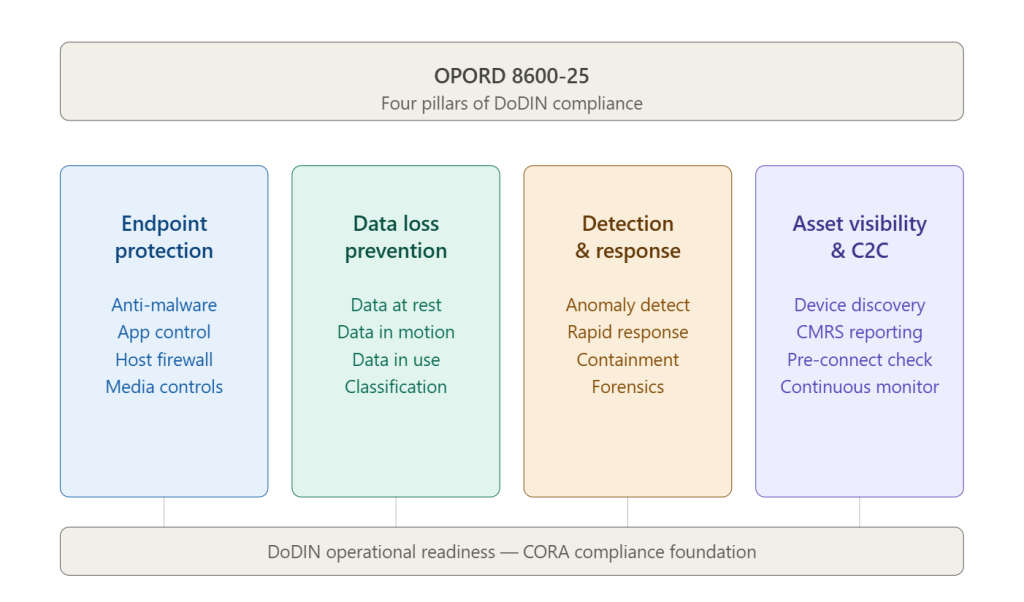
How OPORD 8600-25 Maps to Endpoint Security, Data Loss Prevention (DLP), and Endpoint Detection & Response (EDR)
March 11, 2026
A New Zero-Click Mobile Exploit Is Hitting iPhones. Here’s What DarkSword Means for Federal and DoD Security
March 20, 2026How Current DoD Technologies and Contracts Satisfy OPORD 8600-25
The first two blogs in this series established what OPORD 8600-25 requires and how those requirements map to security capabilities. This final installment answers the question that ultimately drives program decisions: what specific technologies are available today to satisfy each mandate, and how can DoD organizations acquire them efficiently through compliant contract vehicles? The answer, as we will demonstrate, is that the solutions exist, they are proven in DoD environments, and the acquisition pathways are already in place.
OPORD 8600-25 compliance is an operational requirement that must be met now. The organizations that will succeed are those that move from mapping to implementation, deploying technologies that are purpose-built for the DoDIN environment and backed by the contract structures that DoD procurement demands
This Blog Series: OPORD 8600-25 – a Three-Part Guide
- 01 – Understanding OPORD 8600-25: What DoD Organizations Must Know
- 02 – How OPORD 8600-25 Maps to Data Loss Prevention and Endpoint Security
- 03 – How Current Technologies Satisfy OPORD 8600-25 YOU ARE HERE
Data Loss Prevention (DLP)
Data Loss Prevention is the capability area where organizations may face their steepest climb — and where the maturity of available technology has advanced most significantly. A modern DLP solution must do far more than block file transfers. It must discover data it has never been told to look for, classify it intelligently, protect it across all three states simultaneously, and provide the audit trail that CORA inspections require.
The Trellix Data Security ecosystem delivers against all of these requirements. FRC has helped more than 25 government customers through DLP capability maturation using this portfolio. Here is how each component maps to OPORD 8600-25 requirements:
Data Loss Prevention – Full Coverage
- DLP Discover: Automated data discovery and cataloging across networks and file repositories. Satisfies the OPORD requirement to discover, classify, and tag data at rest — you cannot protect what you cannot find, and Trellix DLP Discover eliminates the manual inventory liability that leaves sensitive data exposed.
- DLP Endpoint: Governs data in use and enforces removable media controls with Device Control Management (DCM) and File & Removable Media Protection (FRP). Advanced Visual Labeling for Microsoft Office and Outlook delivers dual-classification labels that satisfy the OPORD’s data tagging and access control requirements. Full IPv6 support ensures compliance with federal modernization mandates.
- Network DLP: Deep content inspection on network traffic satisfies the data-in-motion requirement. The Seamless Web Content Inspection API extends coverage to Microsoft Edge for Business, Mozilla Firefox, and Island browsers — monitoring and blocking unauthorized file uploads and copy/paste actions across all enterprise browsers, a critical control for DoDIN environments.
- AI Data Risk Dashboard: Released December 2025, this capability addresses the emerging insider threat vector created by large language model usage. It provides real-time visibility into sensitive data exposure through AI-related leak vectors such as web browsers — a risk category that did not exist in legacy DLP frameworks but is rapidly becoming a priority for DoD commands.
- Data Encryption: Trellix Drive Encryption and File & Removable Media Protection ensure that any data written to external devices or stored at rest remains encrypted and unreadable to unauthorized parties — directly satisfying the OPORD’s data-at-rest encryption mandate.
- Database Security: Activity monitoring, vulnerability management, and Virtual Patching protect structured data in databases against unauthorized access — extending DLP coverage to the data pillar of Zero Trust architecture without requiring system downtime for patching.
- Trellix ePO: Centralized single-pane-of-glass management across endpoint, network, and cloud DLP deployments. Out-of-the-box compliance reporting maps directly to common frameworks, simplifying the forensic audit trail that CORA inspections require. On-premises, hybrid, and SaaS deployments are managed from a single console.
Consistent with OPORD 8600-25, the DoD Zero Trust Architecture places data at the center of the security universe — every other pillar exists to protect it. A mature DLP solution does not simply block transfers; it educates users in real time, turning accidental policy violations into coaching moments. This behavioral dimension is essential in DoD environments where the insider threat — whether malicious or inadvertent — represents a persistent and significant risk. Trellix’s customizable pop-up notification capability, which prompts users to justify flagged actions before proceeding, directly supports this user-education mandate while preserving the audit record that compliance demands.
Endpoint Detection & Response
The era of signature-based antivirus as a primary endpoint defense is over. Today’s adversaries routinely deploy fileless malware, zero-day exploits, and polymorphic code that leave no conventional signature to detect. Many successful breaches involve no malware at all — attackers authenticate legitimately with compromised credentials and operate entirely within sanctioned tools. OPORD 8600-25’s EDR requirements reflect this reality: static defenses are necessary but insufficient. Behavioral detection, continuous monitoring, and rapid response capability are now baseline requirements.
- Trellix EDR: Continuous telemetry collection and AI-driven behavioral analysis asks not “is this file bad?” but “is this behavior normal?” — detecting anomalies that bypass traditional AV entirely. High-fidelity alerts with contextual threat intelligence reduce analyst fatigue while ensuring that genuine threats are escalated and acted upon with urgency.
- Rapid Response: Remote response actions — endpoint isolation, process termination, file quarantine — are executable directly from the investigation console. This satisfies OPORD 8600-25’s requirement for rapid containment without requiring physical access to affected systems, a critical operational advantage in geographically distributed DoD environments.
- Live Forensics: Timeline reconstruction and evidence preservation enable analysts to understand the full attack chain, close the pathways adversaries used, and prevent recurrence. The DoD Zero Trust framework explicitly requires EDR integration with Comply-to-Connect — Trellix EDR telemetry feeds directly into C2C gateways to enable dynamic access decisions based on real-time endpoint health.
- Trellix XDR: Extended Detection and Response breaks down the silos between endpoint, email, cloud, and network security tools — correlating telemetry across all domains into a unified threat view. An XDR platform can correlate a malicious email attachment alert, a suspicious PowerShell execution on the recipient’s endpoint, and an anomalous cloud access attempt into a single, prioritized incident.
EDR and XDR are not just detection tools — they are data-gathering engines that power a host of Zero Trust capabilities, from dynamic access control to behavioral analytics. For DoD organizations, deploying them is the difference between knowing you have a problem and knowing what to do about it.
Comply-to-Connect
Asset visibility and Comply-to-Connect represent the OPORD 8600-25 pillar that is most directly tied to network access control — and the one where the consequence of failure is most immediate. A non-compliant or unmanaged device that gains access to the DoDIN is not a compliance gap; it is an active threat vector. OPORD 8600-25 requires that every device attempting DoDIN connection be identified, assessed for compliance, and validated for configuration before access is granted.
Cisco Identity Services Engine (ISE), deployed as part of Cisco’s comprehensive DoD Comply-to-Connect bundle, is the industry’s most widely adopted network access and control solution for this requirement. Its C2C architecture maps directly to the DoD’s five-step C2C compliance framework — from initial device discovery through continuous post-connection monitoring.
- Device Discovery: Proactively identifies and inventories every C2C endpoint category — mobile phones, laptops, servers, printers, network infrastructure, IoT devices, weapons systems, and more — across wired, wireless, cloud, and temporarily offline environments. No device connecting to the DoDIN escapes visibility.
- Authentication: Standards-based authentication via 802.1X (a DISA CAT 1 STIG requirement) and MAC Authentication Bypass (MAB) verifies device and user identity before any access is granted. Cisco ISE supports both agentless and agent-based posture assessment, ensuring DoDIN-defined security policies are verified regardless of device type.
- Compliance Posture: Continuous verification that connected devices remain in compliance throughout the entire session — not just at initial connection. ISE takes context from across the entire security stack, integrating with Trellix EDR and other tools to enable dynamic access decisions based on real-time endpoint health. If EDR detects an active threat, ISE can quarantine the device immediately.
- CMRS Reporting: Comprehensive, customizable C2C reporting dashboards consolidate endpoint profile data from all integrated platforms into CMRS-compliant inventory reports. GRC integration is supported when organizations are ready to extend compliance reporting into broader governance frameworks. The C2C Reporting Application Advantage supports all C2C steps through Full Operating Capability (FOC), with the current DoD target of FOC by June 2026.
- Trellix Integration: Cisco ISE and Trellix are not competing solutions — they are complementary layers of the same compliance architecture. Cisco’s advanced C2C training courses explicitly include Trellix as a third-party integration use case. Together, they deliver the device identification, compliance posture, and EDR-informed access control that OPORD 8600-25 requires as an integrated system.
Endpoint Protection: Trellix ENS
Before EDR and XDR can do their work, the foundational endpoint protection layer must be in place. Trellix Endpoint Security (ENS) delivers the anti-malware, application control, and host-based firewall capabilities that OPORD 8600-25’s endpoint protection pillar requires — and it does so as the base layer on which the broader Trellix security architecture is built.
ENS enforces application allowlisting policies that block execution of any software not explicitly authorized — a non-negotiable control for DoDIN environments where unauthorized software represents both a compliance violation and an attack surface. Its host-based firewall operates on a deny-by-default posture, allowing DoDIN connections only by exception, precisely as OPORD 8600-25 mandates. Multi-layered malware prevention combines signature-based detection, behavioral analysis, and machine learning to counter both known and novel threats.
Compliant Acquisition: The Contract Vehicles
Technology capability without an efficient acquisition pathway is, in practice, a compliance delay. For DoD organizations, the good news is that the contract vehicles needed to procure OPORD 8600-25-compliant solutions are already in place — purpose-built for the compliance, pricing, and administrative requirements of DoD procurement.
Vehicle #1 – DoD ESI – Trellix
FRC is a DoD Enterprise Software Initiative (ESI) partner for Trellix, delivering negotiated pricing, compliance assurance, and streamlined procurement for the full Trellix portfolio. DoD ESI eliminates the need for individual price negotiations and ensures that acquired solutions meet DoD security requirements by design.
Vehicle #2 – NASA SEWP V
FRC holds NASA SEWP V contract #NNG15SC61B, providing DoD agencies with access to Trellix and Cisco solutions through one of the federal government’s most widely used and efficiently administered IT acquisition vehicles. SEWP’s competitive pricing and rapid order processing reduce procurement cycle times significantly.
Want to Learn More?
For a deeper operational look at how these technologies perform in a DoD environment, our webinar — Mission Secure: Enabling OPORD 8600 Success with Trellix DLP and EDR — provides the technical and operational context that this blog series has introduced. The recording is available below. Watch our webinar recording or connect with our team to discuss where your organization stands today.



