
OpenClaw: The Reliable AI Agent Orchestrator
May 6, 2026
Continuous Authority to Operate: Why State, Local, and Higher Education Can’t Afford to Wait for the Annual Audit
May 19, 2026The Agencies That Get Zero Trust Right Will Be the Ones Who Did It in the Right Order
The FY 2027 deadline for DoD Zero Trust Target Level compliance is no longer a distant planning horizon. For DoD components still in the early or middle stages of implementation, the window for getting this done right is narrowing. And the difference between those two outcomes often comes down to a single factor that most Zero Trust guidance doesn’t address: sequence.
But the sequencing challenge isn’t unique to DoD. Civilian federal agencies operating under CISA’s Zero Trust Maturity Model and OMB Memorandum M-22-09 face the same dependency gaps. State, local, and higher education institutions adopting Zero Trust frameworks encounter the identical problem: comprehensive guidance on what to implement, and very little on in what order.
That’s the insight behind FRC’s new white paper, Sequencing Zero Trust: A Dependency-Driven Map for Public Sector Implementation and it’s the reason we built something that, to our knowledge, didn’t previously exist in the public sector ZT ecosystem.
What the Framework Tells You and What It Doesn’t
If you’ve spent time with the DoD Zero Trust Strategy, the ZT Overlays publication, or the ZT Execution Roadmap (or their civilian equivalents in CISA’s maturity model and NIST SP 800-207) you know these documents are comprehensive. They define what agencies must achieve with clarity and authority.
What they don’t provide is a clear map of implementation order.
- Which activities must be completed before others can begin?
- Which can proceed in parallel?
- Where does a dependency in the Device pillar create a bottleneck in the Networking pillar?
- Which activities are genuinely independent, and which ones look independent until you’re six months into implementation and discover otherwise?
These are the questions that determine whether your Zero Trust program succeeds on schedule or generates the kind of rework, technical debt, and missed deadlines that are entirely avoidable with better upfront planning. They apply whether you’re a DoD component racing toward FY 2027, a civilian agency building toward full CISA maturity, a state CIO responding to a governor’s cybersecurity executive order, or a university CISO protecting research data and student records under evolving federal compliance requirements.
The Cost of Getting Sequence Wrong
Consider a straightforward example from Pillar 6 Automation & Orchestration. Many agencies are eager to procure SOAR tools early. SOAR is visible, marketable, and easy to point to as evidence of progress. But SOAR tool implementation depends on two predecessor activities being in place first: standardized API calls and schemas, and enriched, context-aware workflows.
Deploy SOAR without those foundations and you’ll have an orchestration platform enforcing incomplete rules against raw, unenriched alerts. The investment doesn’t disappear, but it has to be substantially rebuilt once the prerequisites catch up.
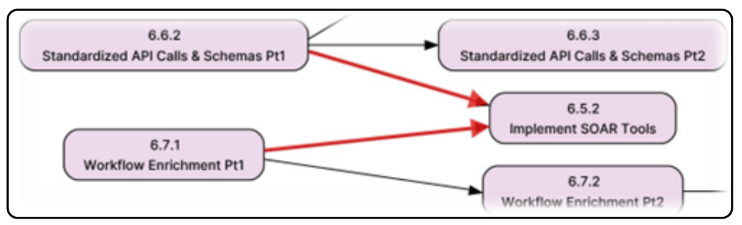
A partial view of the Pillar 6 sequence diagram, showing why SOAR tools cannot be effectively deployed before API standardization and workflow enrichment prerequisites are in place. The full pillar diagram (and all seven diagrams) are available in the white paper.
The same logic applies across all seven pillars. In the Data pillar, DLP and DRM enforcement tools deployed before monitoring infrastructure is in place will produce compliance gaps that don’t surface until an audit. In the Device pillar, XDR capabilities built on an incomplete EDR foundation will underperform until the endpoint layer is solid. In the Application & Workload pillar, Continuous Authorization to Operate (CATO) is a terminal goal, not an early acquisition.
Each of these is a sequencing error. Each is avoidable. And each becomes significantly more expensive to correct the later it is discovered, whether you’re a DoD program office, a civilian agency, or a state IT department operating under tighter budget constraints.
What FRC Built and Why
FRC’s Zero Trust subject matter experts conducted a disciplined analytical synthesis of authoritative DoD source documents to derive the predecessor-successor relationships among all 152 ZT activities across all seven pillars.
The result is a first-of-its-kind set of Zero Trust Activity Sequence Diagrams: seven pillar-specific node diagrams that make the dependency network visible for the first time in a single planning artifact. While derived from DoD’s framework, the sequencing logic these diagrams reveal is applicable to any organization implementing Zero Trust. The dependency relationships between activities don’t change based on which compliance mandate is driving the program.
These diagrams reveal things that lists, tables, and high-level roadmaps cannot:
- Which activities are true starting points (with no prerequisites) and can be initiated immediately and in parallel
- Which activities are trunk nodes whose completion unlocks large downstream chains and whose delay taxes everything that follows
- Where cross-pillar coordination is required activities in one pillar that depend on work being completed in another, signaling that separate teams must be synchronized
- Which activities are genuinely independent representing quick-win opportunities that can be pursued without scheduling risk
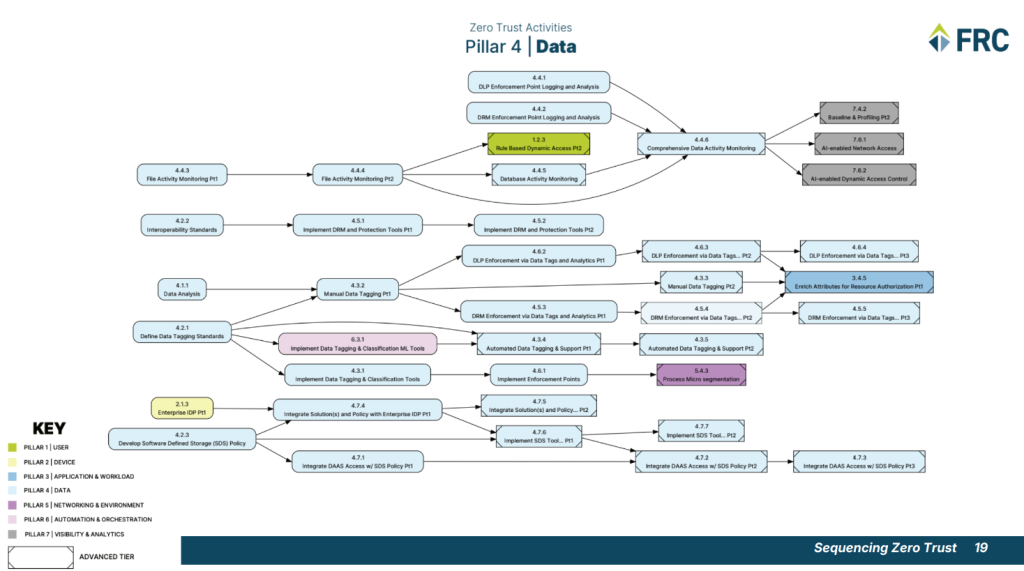
FRC’s Data Pillar sequence diagram, shown here at reduced scale. Full-resolution versions of all seven pillar diagrams are included in the white paper download
For procurement officers and contracting professionals, this translates directly into how you structure task orders, phase budgets, and award contracts. For program managers and CIOs (whether in a federal agency, a state government, or a university IT organization) it means the difference between an implementation plan that builds on itself and one that generates compounding rework.
Where Your Organization Stands and What to Do Next
For DoD components, FY 2027 is the Target Level deadline and FY 2032 the Advanced Level deadline. For civilian agencies, OMB and CISA have established their own maturity timelines. For state, local, and higher education institutions, the pressure comes from a combination of federal funding conditions, state mandates, and the operational realities of an evolving threat environment.
Across all of these, the sequencing challenge is the same and so is the good news: organizations still have time to get this right. The sequence diagrams FRC has developed are designed specifically to support that planning, giving you a dependency-aware map before procurement and execution begin, not after.
Sequencing Zero Trust walks through all seven pillar diagrams, explains the analytical methodology behind them, and translates key sequencing insights into concrete acquisition and planning guidance. It is the resource we wish had existed when public sector organizations first began this journey.
Download the white paper at fedresources.com/zta-sequencing-white-paper-download/ and if you’d like a guided briefing walkthrough with FRC’s Zero Trust subject matter experts, the download page tells you how to request one.
FRC delivers cybersecurity, data, and AI solutions to public sector organizations navigating complex compliance requirements and evolving threat environments. Visit fedresources.com to learn more about our solutions and offerings.



