
Why Zero Trust Needs Automation to Work
September 30, 2025
Zero Trust Commandment: Thou Shalt Consistently Tag Thy Data
October 14, 2025What You Need to Add to your IT Inventory List to Meet Target-Level Zero Trust Posture
IT Inventories and IT Asset Management (ITAM) are a cornerstone of corporate governance. We’ve dutifully tracked serial numbers, purchase dates, assigned owners, and documented installed software. We’ve extended this inventory to include IoT devices and Operational Technology (OT). This inventory gave us a sense of control, a static snapshot of the assets we owned. But in a Zero Trust world, that snapshot is no longer enough. The principle of “never trust, always verify” demands we ask a much more critical question: Is this device healthy enough to be trusted right now?
For an organization to successfully implement Zero Trust, a simple, traditional IT Asset Management (ITAM) list is not sufficient. The foundational work in the Zero Trust Device Pillar demands a dynamic, deeply detailed, and continuously updated asset inventory that goes far beyond managing hardware depreciation or license counts. It requires a system that provides the necessary context for access control.
Gauging Device Health: The Difference-Maker
A traditional ITAM or Configuration Management Database (CMDB) is excellent at answering “what is it?” and “who owns it?”: tracking the lifecycle, location, and ownership of hardware and software for financial, operational, and general compliance purposes. This typically results in a static inventory.
However, it typically cannot answer the questions that are vital for a Zero Trust access decision:
- Is the endpoint detection and response (EDR) agent running and up to date, or has it been disabled?
- Has a critical vulnerability been detected on the device in the last five minutes?
- Is the device compliant with required security configurations, like STIGs, at this very moment?
- Are there any signs of an active compromise, such as malicious processes running in memory?
Answering “yes” to knowing the device’s serial number is fundamentally different from answering “yes” to knowing the device is secure. This is the gap that Zero Trust Activity 2.1.1 – Device Health Tool Gap Analysis is designed to address. The “gap analysis” isn’t just about finding unmanaged devices; it’s about identifying the gap between the static data you have and the dynamic health telemetry you need. This concept is critical because in a Zero Trust model, an access decision is not based on who you are, but also what you are using, and how secure that device is in real-time.
Evolving the Inventory
The inventory data must be continuously enriched and updated with a security posture assessment. Tools that contribute to this include:
- Endpoint Detection and Response (EDR) Tools: These tools provide a continuous stream of telemetry data about a device’s current security status. This includes whether antivirus software is running and updated, if the firewall is active, or if any active threats or vulnerabilities are present.
- Device Posture Assessment Tools: These solutions evaluate a device’s compliance against specific security benchmarks, such as minimum operating system version or the presence of required security agents.
These tools are directly responsible for producing the critical security attributes that indicate device health. For example, a laptop might be an “approved” device in the static ITAM list, but if its EDR tool detects an unpatched, critical vulnerability, its device health status instantly changes to “unhealthy”.
Context is King for the Policy Engine
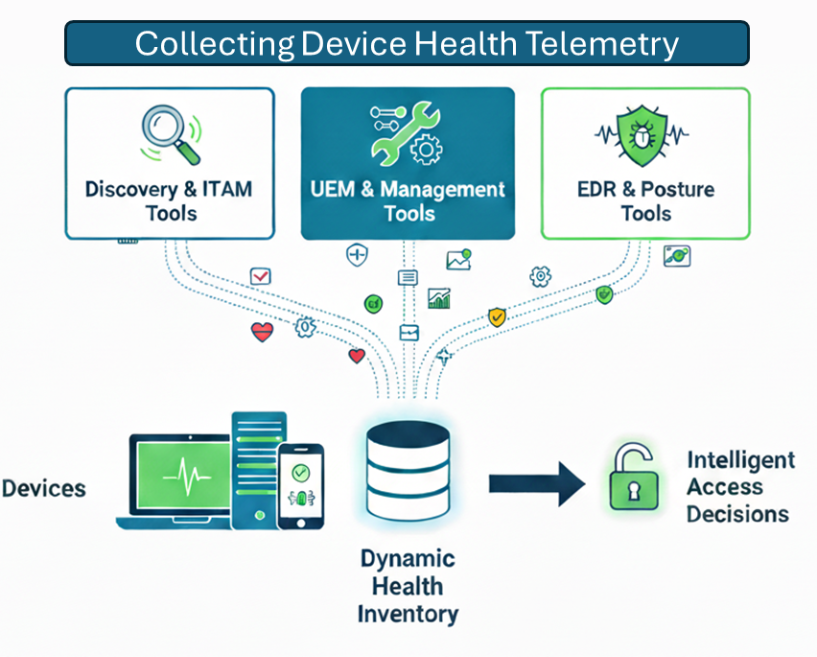
The detailed inventory and the continuous device health status are collected by various solutions—including Device Discovery and ITAM tools, Unified Endpoint Management (UEM/EM) tools, and EDR/Posture Assessment platforms.
The ultimate goal of this deep visibility is to provide the Policy Engine (the decision-maker in the Zero Trust architecture) with all the necessary context. The policy engine will use this inventory and health data to dynamically make access decisions downstream.
For example, a request for highly sensitive data might be automatically approved if the device is:
- On the Authorized Inventory list.
- Showing a “Healthy” status (latest patches, no active threats).
- Associated with the correct owner/department.
If the device is on the inventory but reports an “Unhealthy” status due to a missing patch, the Policy Engine can then apply a granular access restriction, such as limiting the user to read-only access in a segregated environment until the device’s health is remediated.
Securing the Device Access Vector
Successfully establishing this comprehensive visibility and continuous assessment capability is the essential first step in securing the device access vector in a Zero Trust architecture. It is about moving beyond reliance on the network location and gaining granular visibility into the ‘what’ of every access request.
For security professionals, this means procuring and deploying the right combination of device-centric tools—combining agentless discovery for a complete inventory with specialized posture assessment for continuous health monitoring—to establish the technical foundation for device-aware access controls. The Zero Trust Device Pillar requires that security is baked into the very definition of a device, making its health a non-negotiable factor in every access decision.



